Latest Cybersecurity News and Articles
No Patches for Vulnerabilities Allowing Cognex Industrial Camera Hacking
26 September 2025
Cognex is advising customers to transition to newer versions of its machine vision products.
The post No Patches for Vulnerabilities Allowing Cognex Industrial Camera Hacking appeared first on SecurityWeek.
New XCSSET macOS Malware Variant Hijacks Cryptocurrency Transactions
26 September 2025
The malware now uses a four-stage infection chain, has an additional persistence mechanism, and also targets Firefox browser data.
The post New XCSSET macOS Malware Variant Hijacks Cryptocurrency Transactions appeared first on SecurityWeek.
Fortra GoAnywhere CVSS 10 Flaw Exploited as 0-Day a Week Before Public Disclosure
26 September 2025
Cybersecurity company watchTowr Labs has disclosed that it has "credible evidence" of active exploitation of the recently disclosed security flaw in Fortra GoAnywhere Managed File Transfer (MFT) software as early as September 10, 2025, a whole week before it was publicly disclosed.
"This is not 'just' a CVSS 10.0 flaw in a solution long favored by APT groups and ransomware operators – it is a
New macOS XCSSET Variant Targets Firefox with Clipper and Persistence Module
26 September 2025
Cybersecurity researchers have discovered an updated version of a known Apple macOS malware called XCSSET that has been observed in limited attacks.
"This new variant of XCSSET brings key changes related to browser targeting, clipboard hijacking, and persistence mechanisms," the Microsoft Threat Intelligence team said in a Thursday report.
"It employs sophisticated encryption and obfuscation
Recent Fortra GoAnywhere MFT Vulnerability Exploited as Zero-Day
26 September 2025
Eight days before patches, a threat actor exploited CVE-2025-10035 as a zero-day to create a backdoor admin account.
The post Recent Fortra GoAnywhere MFT Vulnerability Exploited as Zero-Day appeared first on SecurityWeek.
Cisco Firewall Zero-Days Exploited in China-Linked ArcaneDoor Attacks
26 September 2025
Leading to remote code execution and privilege escalation, the flaws were exploited on Cisco ASA 5500-X series devices that lack secure boot.
The post Cisco Firewall Zero-Days Exploited in China-Linked ArcaneDoor Attacks appeared first on SecurityWeek.
Cisco ASA Firewall Zero-Day Exploits Deploy RayInitiator and LINE VIPER Malware
26 September 2025
The U.K. National Cyber Security Centre (NCSC) has revealed that threat actors have exploited the recently disclosed security flaws impacting Cisco firewalls as part of zero-day attacks to deliver previously undocumented malware families like RayInitiator and LINE VIPER.
"The RayInitiator and LINE VIPER malware represent a significant evolution on that used in the previous campaign, both in
Hackers reportedly steal details of 8,000 children from Kido nursery chain
25 September 2025
 Firm, which has 18 sites around London and more in US, India and China, has received ransom demand, say reportsThe names, pictures and addresses of about 8,000 children have reportedly been stolen from the Kido nursery chain by a gang of cybercriminals.The criminals have demanded a ransom from the company – which has 18 sites around London, with more in the US, India and China – according to the BBC. Continue reading...
Firm, which has 18 sites around London and more in US, India and China, has received ransom demand, say reportsThe names, pictures and addresses of about 8,000 children have reportedly been stolen from the Kido nursery chain by a gang of cybercriminals.The criminals have demanded a ransom from the company – which has 18 sites around London, with more in the US, India and China – according to the BBC. Continue reading...
Keir Starmer expected to announce plans for digital ID cards
25 September 2025
 As government looks for ways to tackle illegal immigration, move will spark battle with civil liberties campaignersAll working adults will need digital ID cards under plans to be announced by Keir Starmer in a move that will spark a battle with civil liberties campaigners.The prime minister will set out the plans on Friday at a conference on how progressive politicians can tackle the problems facing the UK, including addressing voter concerns around immigration. Continue reading...
As government looks for ways to tackle illegal immigration, move will spark battle with civil liberties campaignersAll working adults will need digital ID cards under plans to be announced by Keir Starmer in a move that will spark a battle with civil liberties campaigners.The prime minister will set out the plans on Friday at a conference on how progressive politicians can tackle the problems facing the UK, including addressing voter concerns around immigration. Continue reading...
Urgent: Cisco ASA Zero-Day Duo Under Attack; CISA Triggers Emergency Mitigation Directive
25 September 2025
Cisco is urging customers to patch two security flaws impacting the VPN web server of Cisco Secure Firewall Adaptive Security Appliance (ASA) Software and Cisco Secure Firewall Threat Defense (FTD) Software, which it said have been exploited in the wild.
The zero-day vulnerabilities in question are listed below -
CVE-2025-20333 (CVSS score: 9.9) - An improper validation of user-supplied input
Digital ID cards: a versatile and useful tool or a worrying cybersecurity risk?
25 September 2025
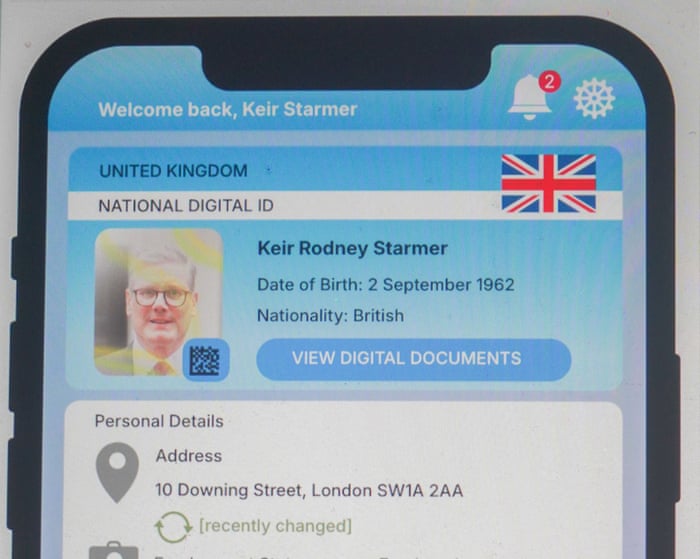 As Keir Starmer aims to revive ID card system first proposed by Tony Blair, we look at the arguments for and againstIt is 21 years since Tony Blair’s government made proposals for an ID card system to tackle illegal working and immigration, and to make it more convenient for the public to access services.The same issues are on the agenda again as Keir Starmer revives what became one of New Labour’s most controversial policies. He is about to find out if he can defeat the argument that David Cameron’s Conservatives made before scrapping it. They said the ID card approach to personal privacy was “the worst of all worlds – intrusive, ineffective and enormously expensive”. Continue reading...
As Keir Starmer aims to revive ID card system first proposed by Tony Blair, we look at the arguments for and againstIt is 21 years since Tony Blair’s government made proposals for an ID card system to tackle illegal working and immigration, and to make it more convenient for the public to access services.The same issues are on the agenda again as Keir Starmer revives what became one of New Labour’s most controversial policies. He is about to find out if he can defeat the argument that David Cameron’s Conservatives made before scrapping it. They said the ID card approach to personal privacy was “the worst of all worlds – intrusive, ineffective and enormously expensive”. Continue reading...
Vane Viper Generates 1 Trillion DNS Queries to Power Global Malware and Ad Fraud Network
25 September 2025
The threat actor known as Vane Viper has been outed as a purveyor of malicious ad technology (adtech), while relying on a tangled web of shell companies and opaque ownership structures to deliberately evade responsibility.
"Vane Viper has provided core infrastructure in widespread malvertising, ad fraud, and cyberthreat proliferation for at least a decade," Infoblox said in a technical report
NCSC statement following reports of nursery data incident
25 September 2025
Statement from the NCSC in response to reports of an incident impacting nurseries.
Salesforce AI Hack Enabled CRM Data Theft
25 September 2025
Prompt injection has been leveraged alongside an expired domain to steal Salesforce data in an attack named ForcedLeak.
The post Salesforce AI Hack Enabled CRM Data Theft appeared first on SecurityWeek.
Salesforce Patches Critical ForcedLeak Bug Exposing CRM Data via AI Prompt Injection
25 September 2025
Cybersecurity researchers have disclosed a critical flaw impacting Salesforce Agentforce, a platform for building artificial intelligence (AI) agents, that could allow attackers to potentially exfiltrate sensitive data from its customer relationship management (CRM) tool by means of an indirect prompt injection.
The vulnerability has been codenamed ForcedLeak (CVSS score: 9.4) by Noma Security,
PyPI Warns Users of Fresh Phishing Campaign
25 September 2025
Threat actors impersonating PyPI ask users to verify their email for security purposes, directing them to fake websites.
The post PyPI Warns Users of Fresh Phishing Campaign appeared first on SecurityWeek.
North Korean Hackers Use New AkdoorTea Backdoor to Target Global Crypto Developers
25 September 2025
The North Korea-linked threat actors associated with the Contagious Interview campaign have been attributed to a previously undocumented backdoor called AkdoorTea, along with tools like TsunamiKit and Tropidoor.
Slovak cybersecurity firm ESET, which is tracking the activity under the name DeceptiveDevelopment, said the campaign targets software developers across all operating systems, Windows,
Chinese Cyberspies Hacked US Defense Contractors
25 September 2025
RedNovember has been targeting government, defense and aerospace, and legal services organizations worldwide.
The post Chinese Cyberspies Hacked US Defense Contractors appeared first on SecurityWeek.
RTX Confirms Airport Services Hit by Ransomware
25 September 2025
The aerospace and defense giant has disclosed the cyberattack in a filing with the SEC.
The post RTX Confirms Airport Services Hit by Ransomware appeared first on SecurityWeek.
Perspective: Why Politics in the Workplace is a Cybersecurity Risk
25 September 2025
Bringing politics into professional spaces undermines decision-making, collaboration, and ultimately weakens security teams.
The post Perspective: Why Politics in the Workplace is a Cybersecurity Risk appeared first on SecurityWeek.